Set Air Headphones in Box, Cyber Security, Internet of Things, SSD Card, Virtual Reality, Gamepad, Router and Wi-fi Stock Vector - Illustration of icon, wireless: 231669607
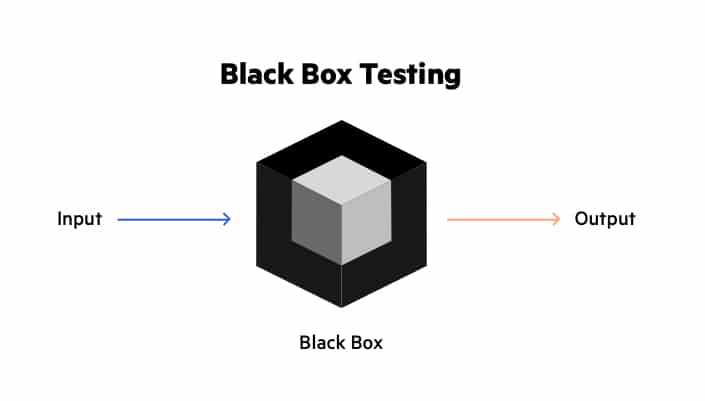
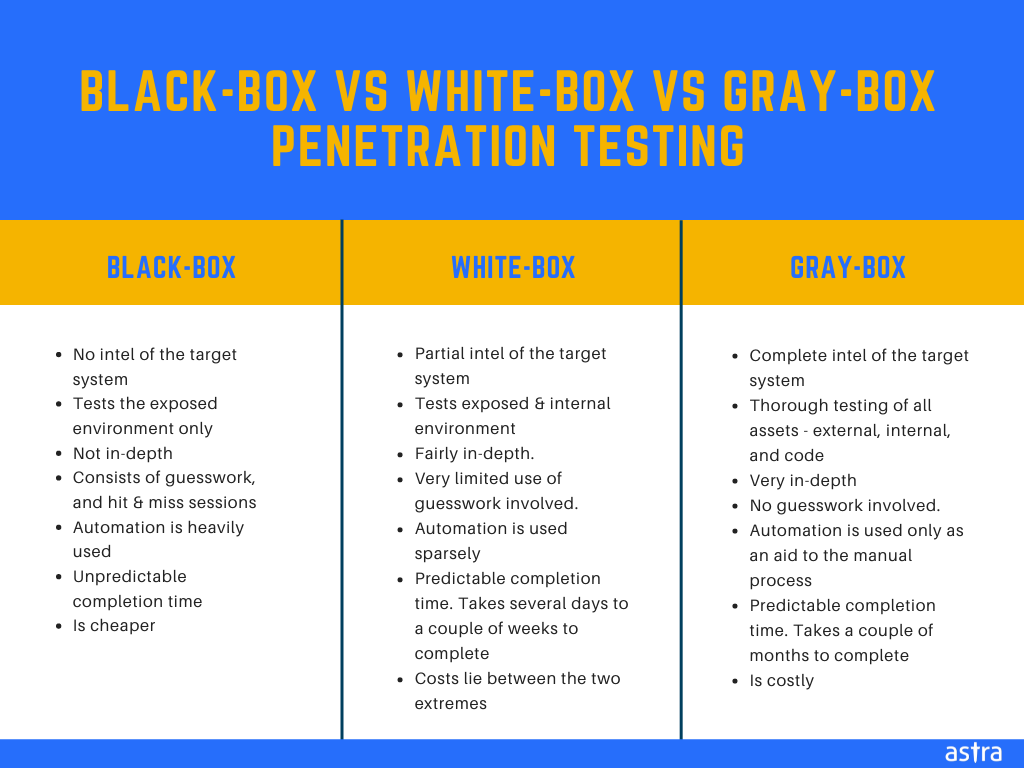
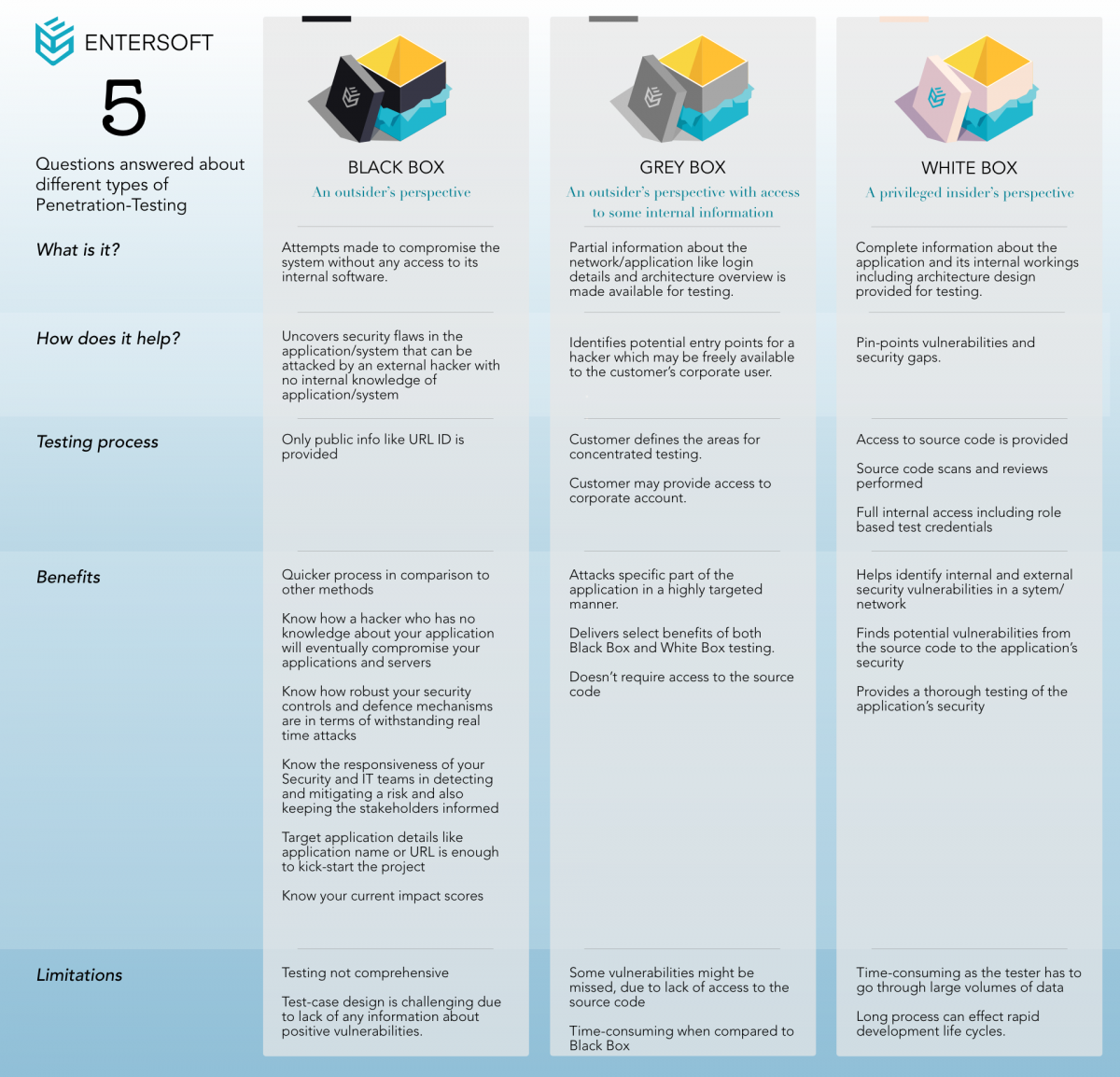
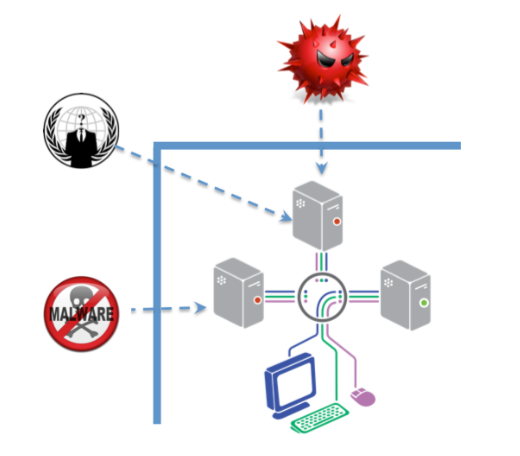
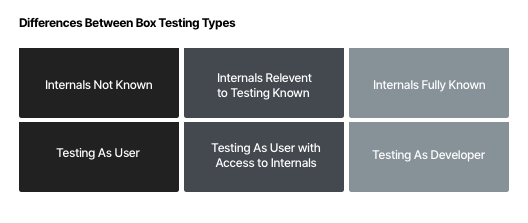
Black Box Attacks on Explainable Artificial Intelligence(XAI) methods in Cyber Security · Issue #6 · hbaniecki/adversarial-explainable-ai · GitHub